Exploitedcollegegirls Excogi Ellie Hazel Top Instant
Secure, scalable, and game-changing authentication for your applications. Get started in minutes with our powerful APIs and SDKs.

Secure, scalable, and game-changing authentication for your applications. Get started in minutes with our powerful APIs and SDKs.

Integrate into any programming language

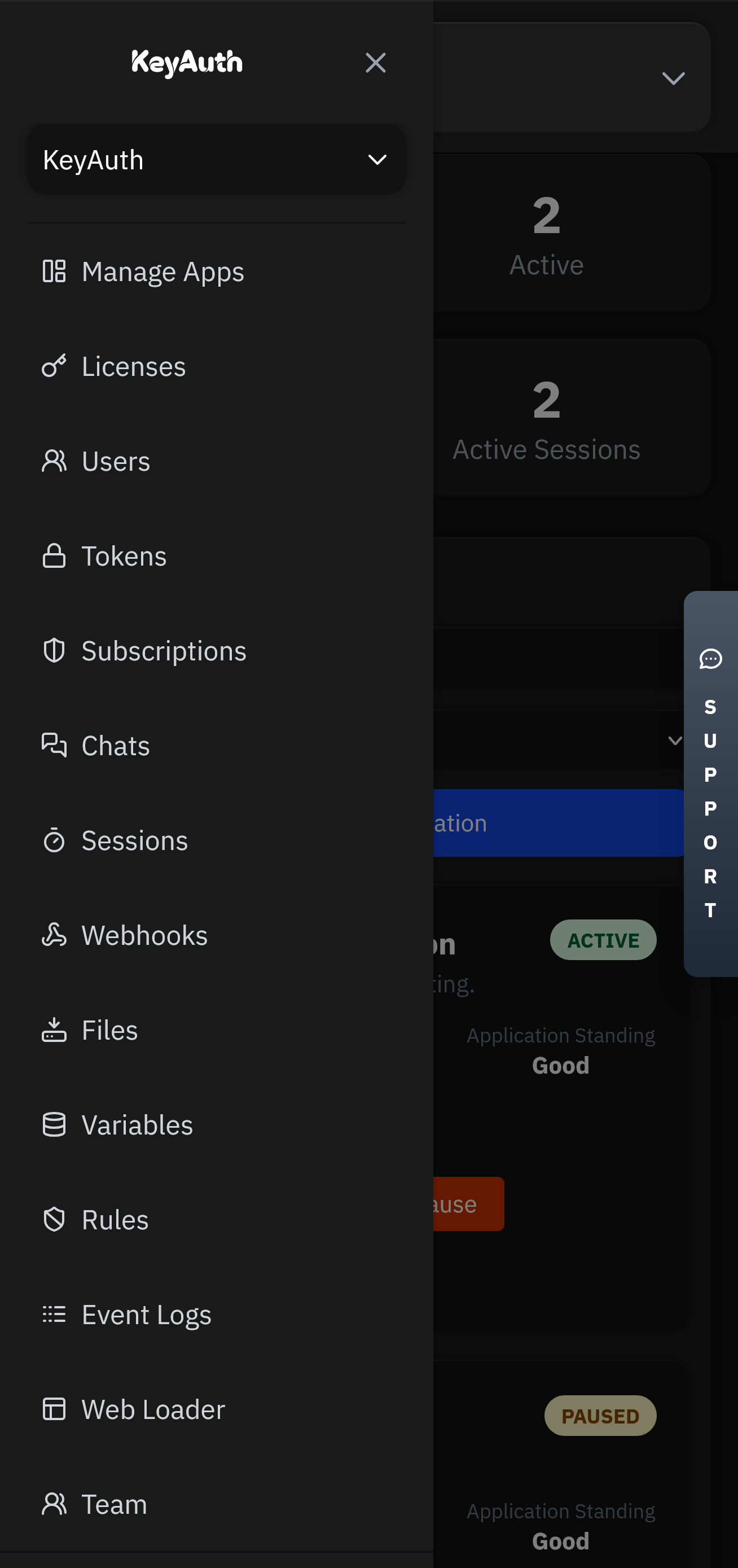
A comprehensive suite of integrated tools for authentication, monetization, and user engagement.
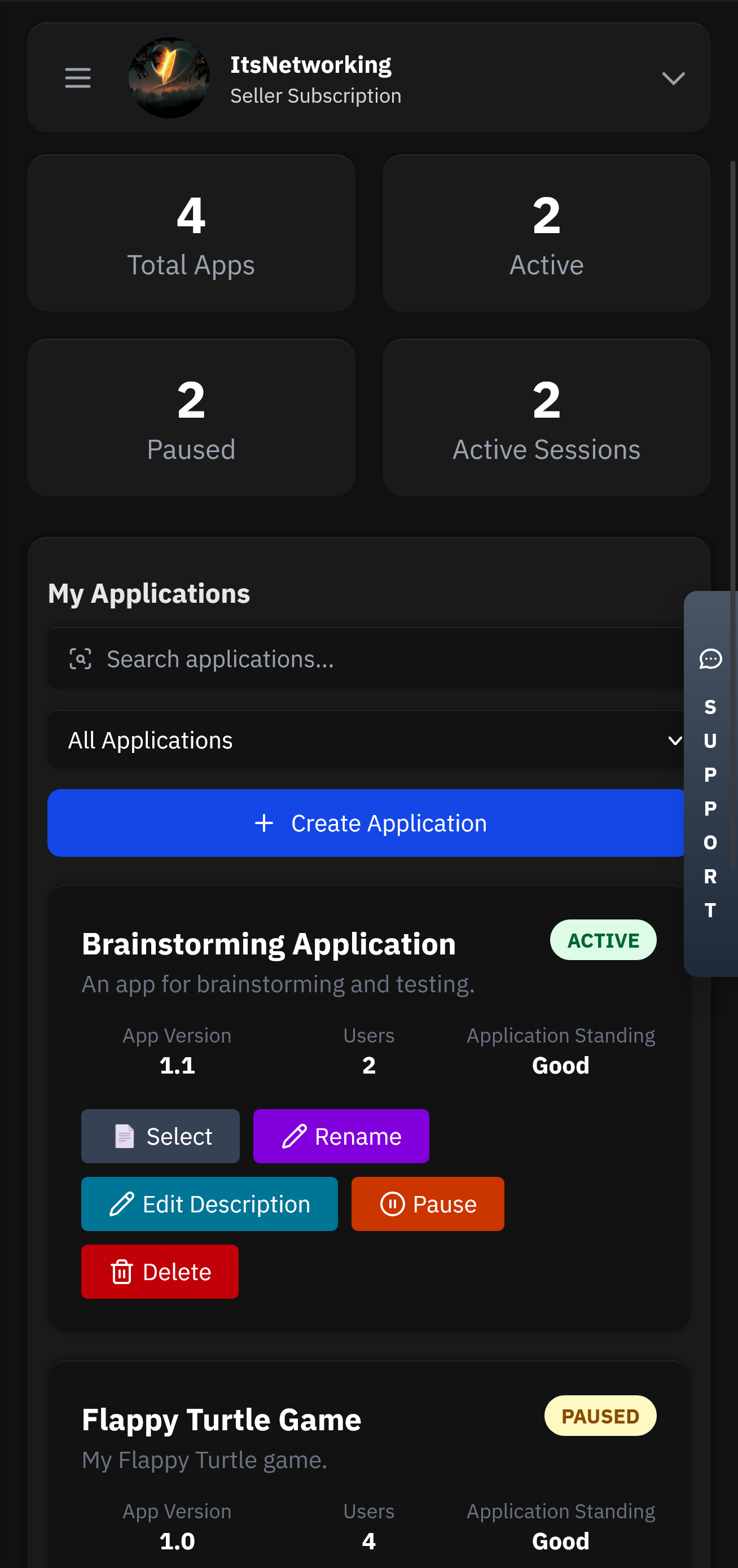
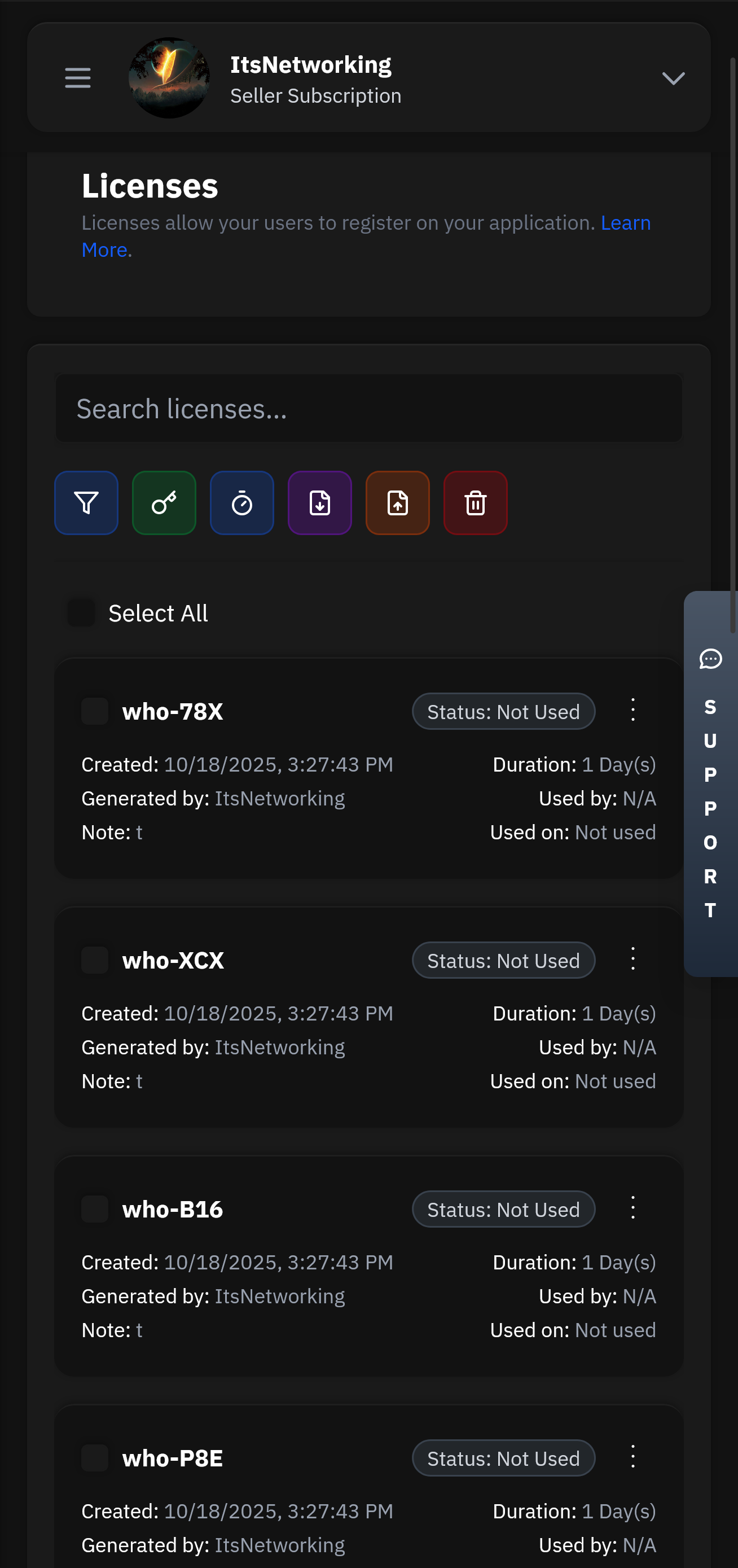
Create and manage user licenses with flexible expiration, trial, and subscription options.
Our lightning-fast infrastructure ensures your authentication requests are processed in under 50ms globally. With 99.99% uptime and redundant systems, your users will never experience delays.
Manage your applications remotely with our powerful Seller API. Update licenses, ban users, modify subscriptions, and monitor usage from anywhere in the world with full administrative control.
Built on a serverless architecture that automatically scales to handle millions of requests. Our global edge network ensures low latency and high availability across 300+ locations worldwide.
There's no question as to why we are the best choice for your business and one of the most used Authentication services.
Head over to our register page to create your account.
Applications will be the heart of your service. This is where all your users, licenses, chats and more will be stored.
Head over to our GitHub to find our examples and client API files. Simply follow the steps and have authentication up in less than 5 minutes.
Control your application from anywhere using our mobile app. Manage licenses, chat with users, and view analytics directly from your phone or tablet.
Flexible options for teams of all sizes.
Excogi is another platform that has been criticized for its role in the objectification and exploitation of women. The site, which allows users to upload and share explicit content, has been accused of promoting a culture of objectification and exploitation. A critical examination of Excogi reveals a platform that prioritizes profit over the well-being and safety of its users, particularly women.
The cases of Ellie and Hazel, two individuals who have spoken out about their experiences with online exploitation, highlight the human impact of this issue. Ellie and Hazel's stories demonstrate the complexities of online exploitation, including the role of social media, online platforms, and societal attitudes. Their experiences also underscore the need for a comprehensive approach to address online exploitation, including education, support services, and policy changes.
The exploitation of women and girls online is a complex issue that requires a comprehensive approach. The cases of ExploitedCollegeGirls, Excogi, Ellie, and Hazel highlight the need for a critical examination of online platforms and their role in perpetuating exploitation. By understanding the complexities of online exploitation, we can work towards creating a safer and more supportive online environment for all individuals.
The exploitation of women and girls online is a pervasive issue that affects millions of individuals worldwide. Online platforms, such as social media and websites, have created new avenues for exploiters to target and manipulate vulnerable individuals. The cases of ExploitedCollegeGirls, Excogi, Ellie, and Hazel highlight the complexities of online exploitation and the need for a comprehensive approach to address this issue.
The rise of online platforms and social media has led to a significant increase in the exploitation of individuals, particularly women and girls. This essay aims to critically examine the phenomenon of online exploitation, focusing on the cases of ExploitedCollegeGirls, Excogi, Ellie, and Hazel.



Got questions? We've got answers. If you can't find what you're looking for, feel free to reach out to our support team.